Helpful Videos
How to Spot Phishing Scams and Avoid Dangerous Links
Understanding Ransomware: How It Works and How to Prevent It
Password Best Practices: Building Strong, Secure Passwords
Downloads - Grid

Cybersecurity Essentials: A Beginner’s Guide to Protecting Your Business
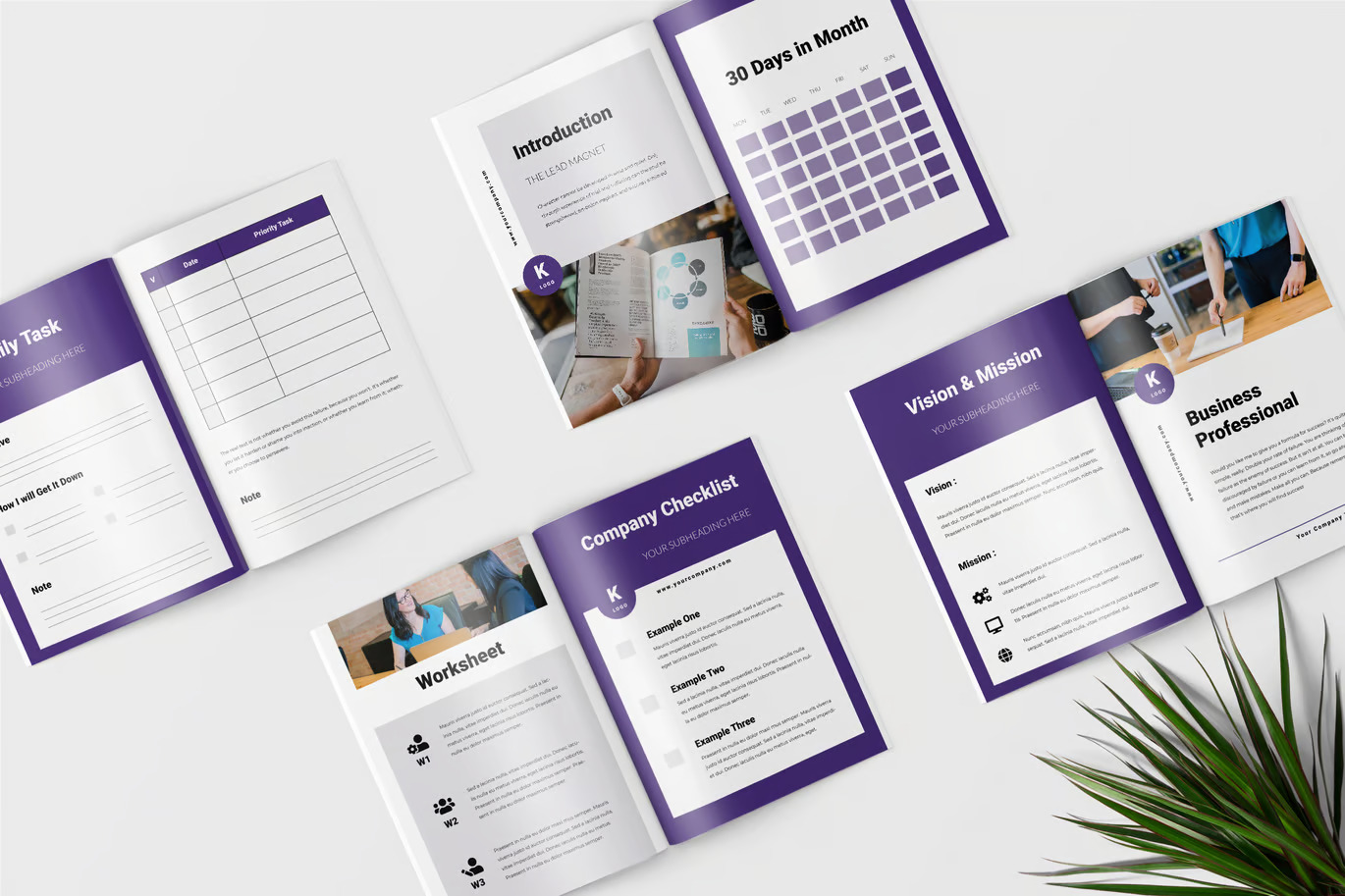
The Cybersecurity Toolkit for Small Businesses
The Incident Response Playbook: Be Prepared for Any Cyber Attack
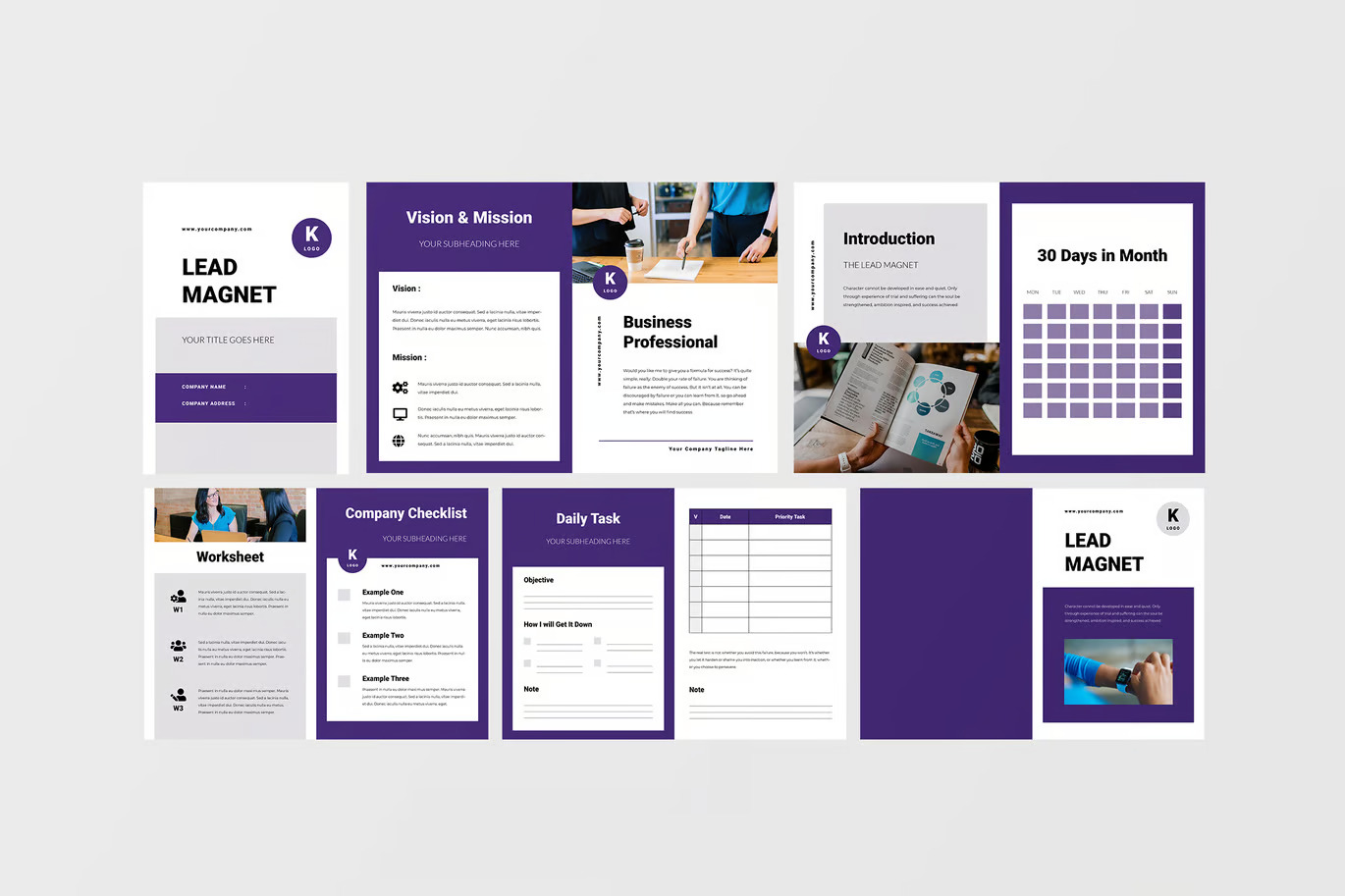
Downloads - Column
Cybersecurity: A Beginner’s Guide to Protecting Your Business
Get started with foundational cybersecurity practices that every business should implement to safeguard against common threats and minimize risk.
The Cybersecurity Toolkit for Small Businesses
A comprehensive toolkit of strategies, templates, and checklists tailored for small businesses to build a strong cybersecurity foundation.
The Incident Response Playbook: Be Prepared for Any Cyber Attack
Equip your team with a detailed playbook to quickly and effectively respond to security breaches, minimize damage, and keep your operations running smoothly.
Tools
Wireshark
A network protocol analyzer that captures and inspects data traveling through a network in real-time, helping identify vulnerabilities and troubleshoot network issues.
Metasploit
An open-source penetration testing framework that allows security professionals to test system defenses, find weaknesses, and improve security by simulating attacks.
Nmap (Network Mapper)
A network scanning tool used for discovering devices on a network, scanning for open ports, and identifying vulnerabilities, often used in network audits and security assessments.
Kali Linux
A Debian-based Linux distribution with a suite of pre-installed security tools for penetration testing, forensics, and reverse engineering, commonly used by cybersecurity professionals.
Let's Put Your Cybersecurity Concerns To Rest
You can't afford to spend your days worrying about your business and whether it's secure. Let us take care of your cybersecurity so you can focus on managing your team, gaining clients, and growing your business.
Call (785) 377-5382 today or click the button below to book an introductory call. We’re ready to secure your IT systems.
